Evidence
Interface & evidence
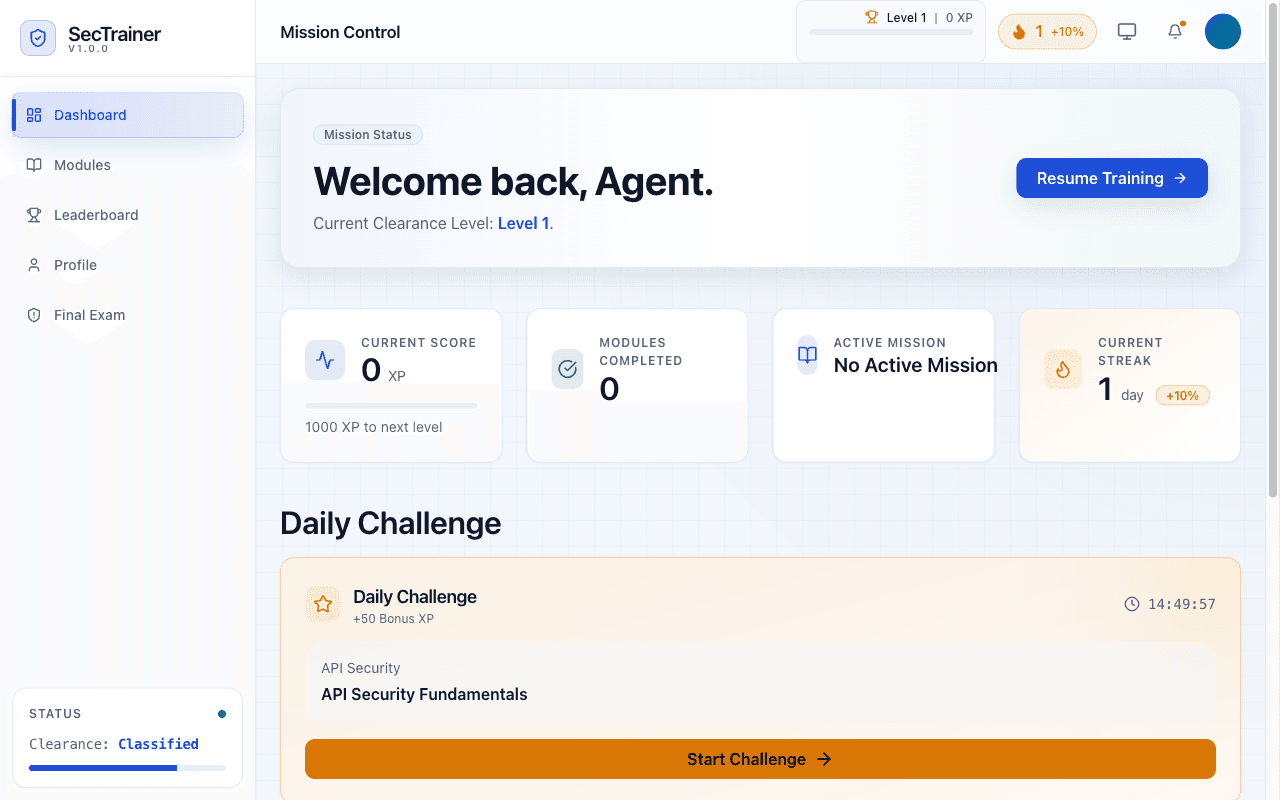
A real surface area—not a mock. Scroll the story below for constraint, build, and outcome.
Story arc
How this shipped
Building the tools that build the toolsThree beats: what pressed against the work, how the stack answered, and what changed once it was live.
I · Constraint
The brief
Security training is often theoretical and boring. Developers learn best by doing, but vulnerability labs are complex to set up.
II · Build
The craft
Built sandboxed vulnerability simulations developers can exploit safely. Hands-on exercises teach OWASP Top 10 through practice.
III · Proof
What moved after launch
Hands-on exercises increase retention 3x vs reading. Sandboxed environments eliminate setup friction. Progress tracking identifies knowledge gaps.
Inventory