Evidence
Interface & evidence
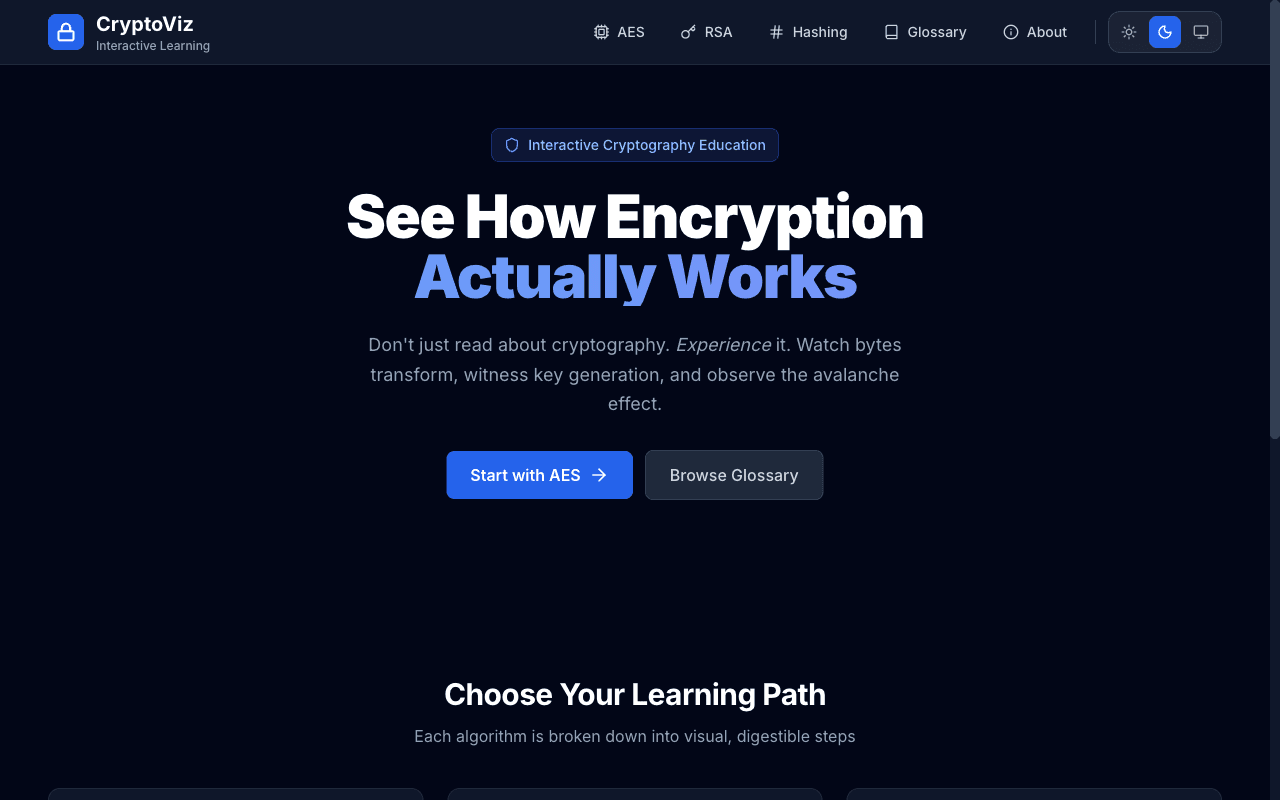
A real surface area—not a mock. Scroll the story below for constraint, build, and outcome.
Story arc
How this shipped
Building the tools that build the toolsThree beats: what pressed against the work, how the stack answered, and what changed once it was live.
I · Constraint
The brief
Making complex cryptographic algorithms understandable through visualization rather than abstract mathematics.
II · Build
The craft
Built step-by-step animated visualizations showing how AES, RSA, and SHA algorithms transform data. Interactive controls let users see each operation.
III · Proof
What moved after launch
Visualizes 5 major encryption algorithms. Used as educational resource by security-focused developers. Real-time byte-level transformation display.
Inventory